Case Study
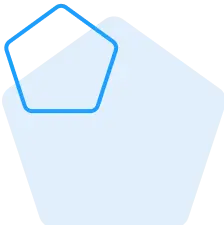
Vulnerability Scan
Compliance Scan
Codenomicon Defensics
Web Application Scan
- System under test: Carrier VoIP Provisioning Portal Server which is a Web UI provides secure subscriber provisioning, device provisioning, system resource management, etc…
- Test method: Credential on
- Test category: Web Application
- Tools used: Nessus
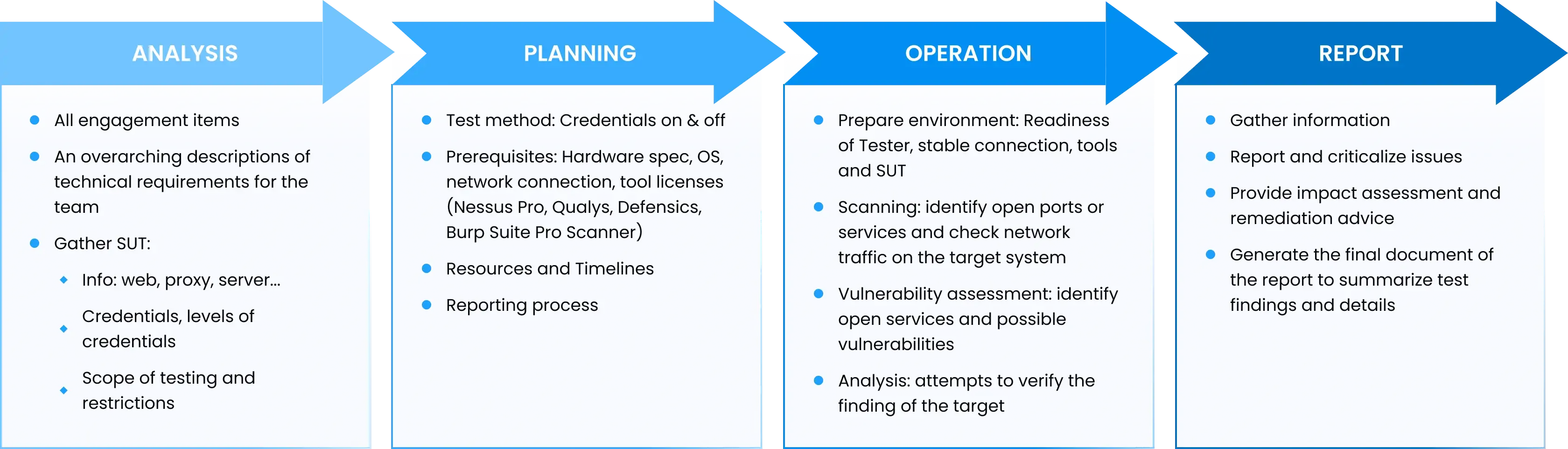
Test Procedure:
- Execute vulnerability scanning against the target
- Generate scan reports
- Check for real issue
Summary of issues found:
- RPM package updates
- TLS vulnerable version
- Apache Log4j
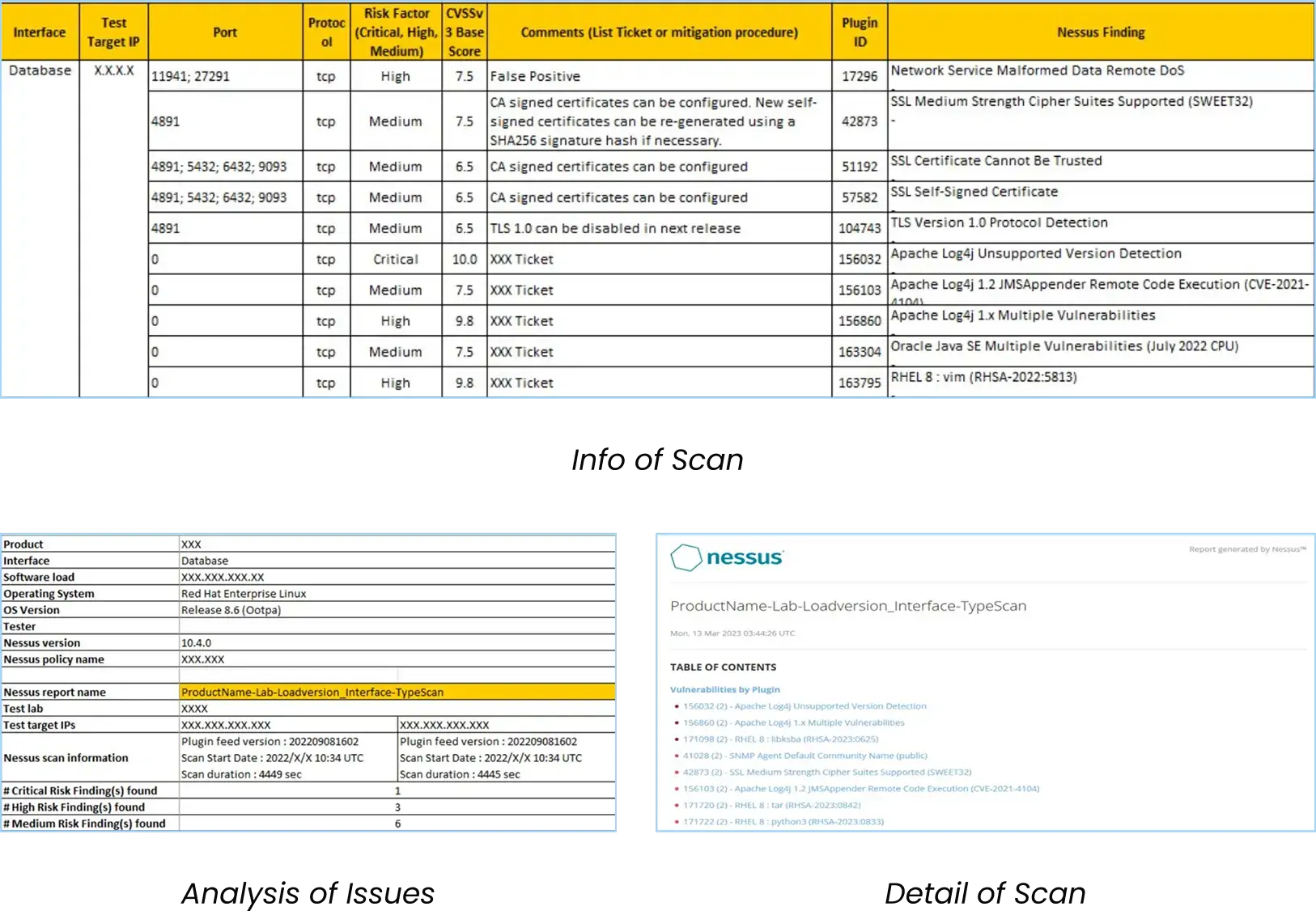
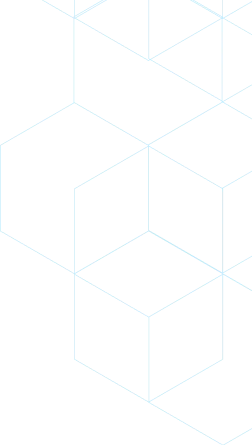
- System under test: Media Server which is a Linux system provides media processing functions, system resource management, etc…
- Test method: Credential on
- Test category: System Compliance
- Tools used: Nessus
Test Procedure:
- Execute OS Compliance scan against target
- Generate scan reports
- Check for real issues of failed compliance items
Summary of issues found:
- Compliance Failure Items of system
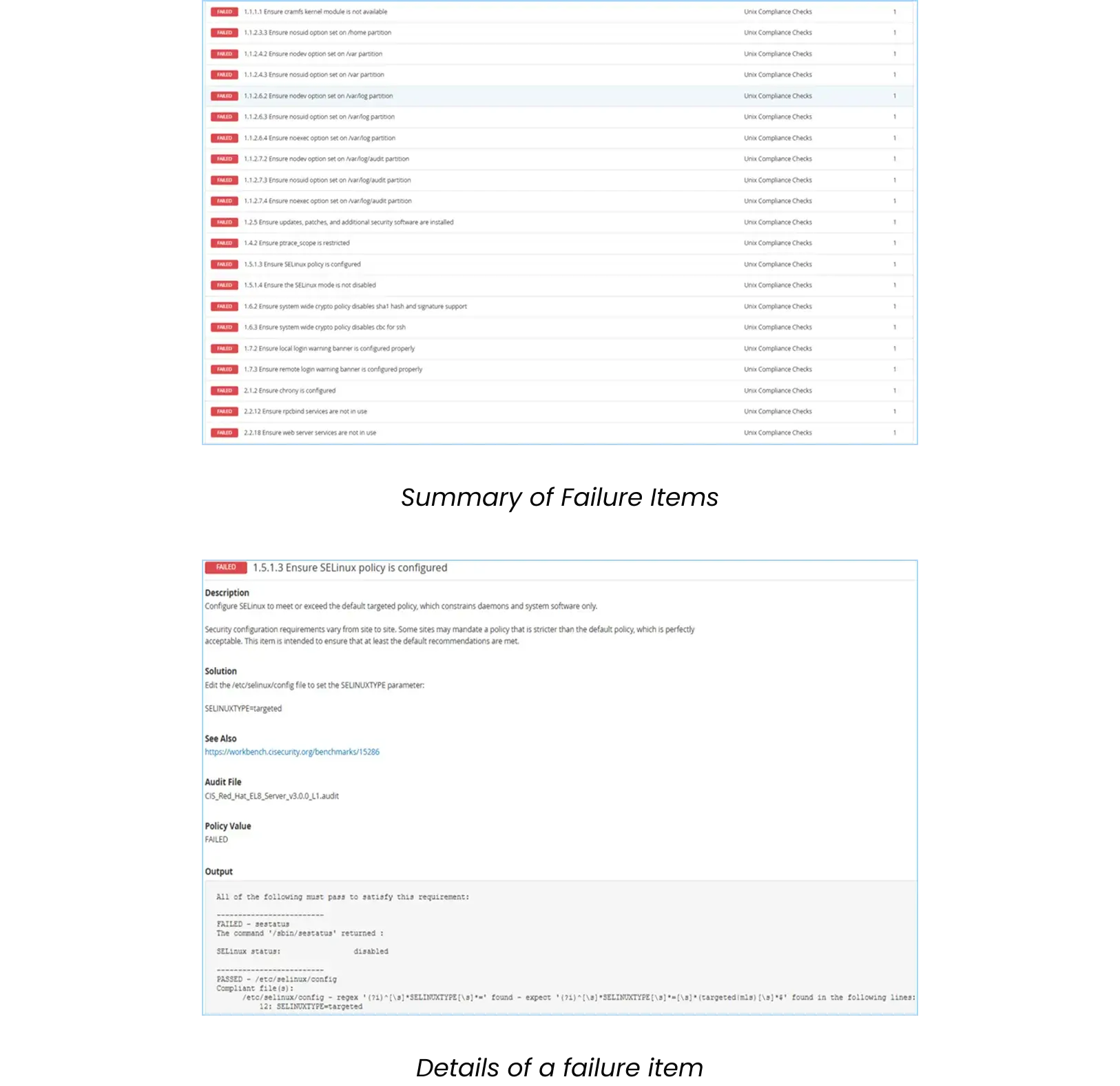
- System under test: Carrier VoIP Server which provides secure SIP calls
- Test method: Credential on
- Test category: Call Server
- Tools used: Codenomicon Defensics
Test Procedure:
- Setup SIP UAS message with Invite-Bye call
- Run the suite with randomized anomalies
- Check the behavior of target to the anomaly messages
Summary of issues found:
- Target switch activity to standby unit since it can’t handle anomaly in Record-Route header
- Target response improperly to the valid anomaly in Call-ID according to SIP RFC
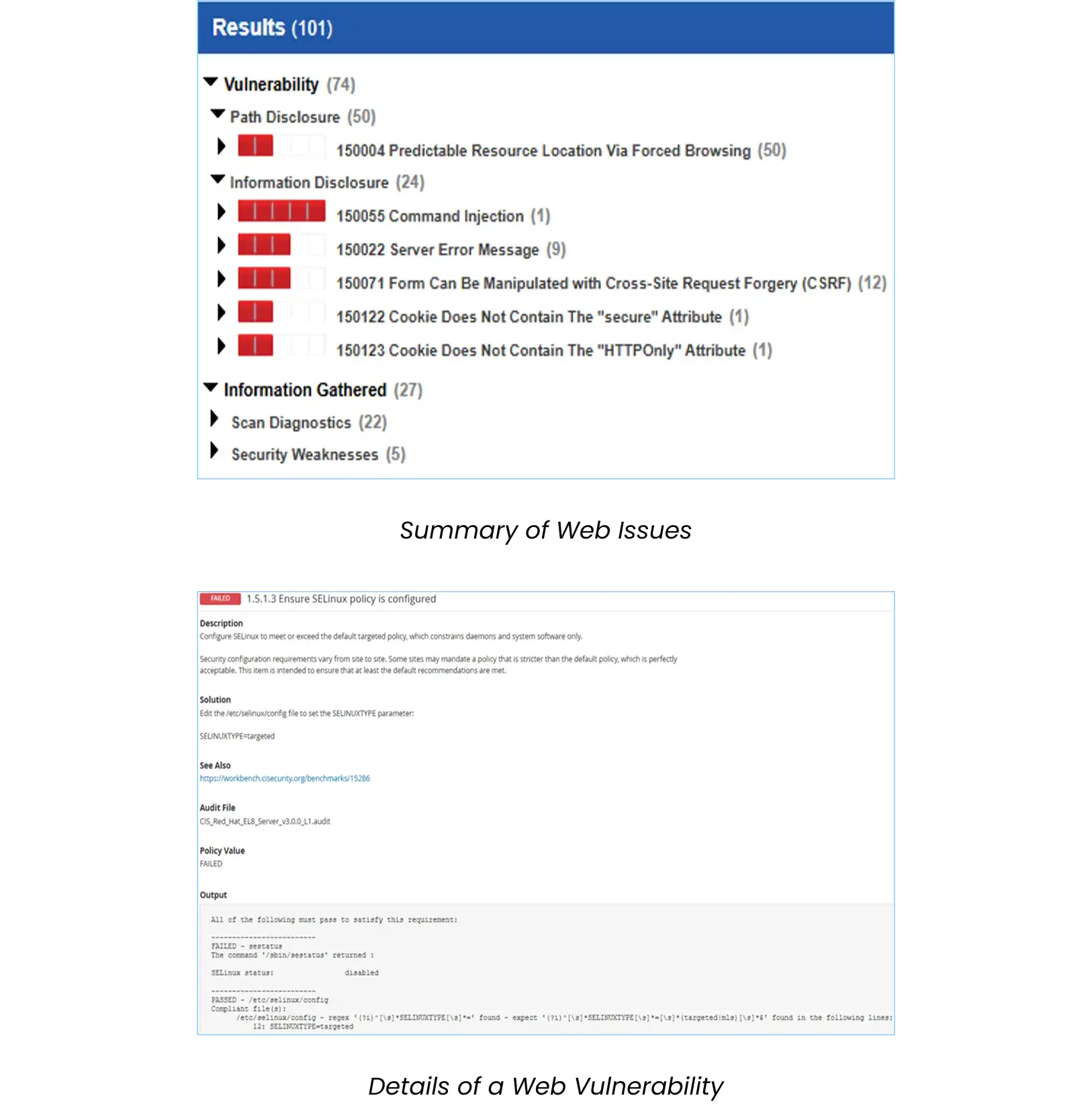
- System under test: Call-Signaling Processing Server which is a Web UI provides signaling processing of call, secure subscriber provisioning, call routing, etc…
- Test method: Credential on
- Test category: Web Application
- Tools used: Qualys
Test Procedure:
- Execute Web Application scan against target
- Generate scan reports
- Check for real issues
Summary of issues found:
- Command Injection
- Cross-site Request Forgery
- Cookie Missing Security Attributes